Executive-Level IT Consulting on Campus: General and Personal Notes
Fresh eyes are important: they see differently, uncover issues, broaden perspective, clarify thinking, suggest alternatives. This is why cross-cutting teams are so important to successful IT management and innovation. It’s also one reason to use consultants. But not the only one.
By “consultants” I don’t mean outsiders who are contracted to operate a service, implement a system, or otherwise do regular IT work; those I think of as “contractors”. (The language is imperfect, to be sure: those we contract with to do regular IT work often call themselves consultants, and those I think of as consultants often work technically as contractors. But this distinction between “consultant” and “contractor” seems reasonably clear, so I’ll stick with it.)
Purposes
In my experience, in or around higher-education IT we use consultants for several purposes. It’s important not to confuse them, because arguably different purposes call for different kinds of consultants and engagements. I suggest there are at least five distinct categories: Implementation, Advice, Evaluation, Scrutiny, and Leadership.
Implementation. Consultants can play roles at various points as projects or services are conceived, developed, and implemented. They can assist with design, either of entire projects or of key elements: for example, if a campus is implementing a new parking system that authenticates electronic parking cards, collects parking fees, and interconnects its kiosks and gateways over the campus network, a consultant might help design the entire system, or might focus on a particularly vexing component such as ensuring that the system’s network use is PCI compliant (that is, encrypts credit-card information appropriately). Or they can critique how campus staff have designed an entire system or any of its components. They can help IT staff and their campus partners identify appropriate vendors, screen them, and make a good choice. Finally, they can provide oversight as a project goes forward or a service is implemented.
Advice. In this domain consultants bring expertise and experience to bear on various dimensions of campus IT, its organization, or the challenges it faces. I include hiring advice in this category, including both general guidance as to how positions should be specified and filled and more specific guidance such as that provided by search consultants. The category includes advice on how to organize IT, on how to describe and advocate its financing, or on other structural matters. And it also includes advice on campus IT policy, including both exogenously-driven policies ensuring campus compliance with federal and state law and endogenously-driven policies ensuring, for example, that IT is treated consistently with other campus resources insofar as acceptable use, disciplinary processes, and penalties are concerned.
Evaluation. Consultants can help IT organizations evaluate various dimensions of their activity internally (evaluation of IT organizations, staff, or function by outsiders is the next category, Scrutiny). Consultants can appraise the overall catalog of IT services and functions, or they can appraise individual services. Consultants can evaluate specific individuals, or the overall entity’s organization or effectiveness. Finally, consultants can provide benchmarks for IT staffing, spending, or service levels.
Scrutiny. As my friend and colleague Brian Voss has written with some passion, senior campus leaders often don’t understand IT. (I’ve written a followup to his piece.) Yet they know it’s important, and that it consumes substantial campus resources, and so sometimes seek external help to evaluate campus IT, usually from consultants. These engagements generally start with analysis of how campus IT functions, including the array, effectiveness, and cost of IT services. They usually go on to examine the organization of IT on campus, and especially the balance among central, departmental, and other IT providers. And quite frequently the engagement ends up focusing on IT leadership, specifically whether the CIO (whatever his or her title) is well aligned with what the campus needs.
Leadership. Finally, and importantly if rarely, consultants sometimes provide leadership for campus IT. This can take three overlapping forms: consultants can outsource leadership through long-term arrangements, such as Collegis does for many campuses; they can provide temporary leadership while a campus searches for a permanent candidate, as the aforementioned Voss did for Case Western Reserve; or they can provide supplementary leadership for a CIO who has become overloaded, undertaken a temporary assignment elsewhere on campus, faces an unexpected set of challenges, or otherwise needs extra hands, heads, and help to get through a taxing time, transition, or project.
Types
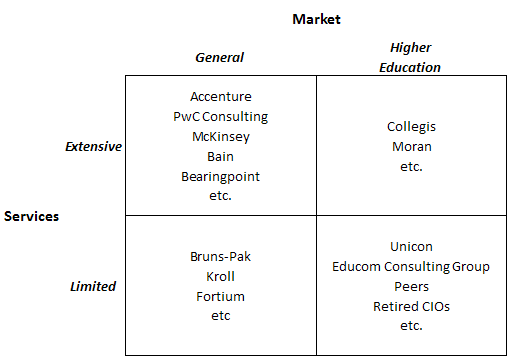
As I suggested above, different uses of consultants call for different types of consultants. Here again there are usefully distinct categories to think about:
- Firms that market an extensive array of consulting, implementation, and other services across general markets, such as majors like Accenture, PwC Consulting, McKinsey, and Bain.
- Firms that offer similarly extensive services but focus on higher education, such as Collegis and Moran.
- Firms that focus in a limited area, such as Bruns-Pak for data-center design or Kroll for security, across general markets.
- Firms that focus on a limited area and on higher education, such as Unicon for Web portals on campuses.
- Individuals who consult freelance, usually with limited focus, in higher education–often retired CIOs.
- Individuals working in limited areas for general markets or in higher education through formal or informal consulting groups.
An early (if unsuccessful) example of that last in higher education was the Educom Consulting Group. A current general-market example (promo alert!) is Fortium Partners, which consists largely of consultants with years of experience as CIOs in diverse industries, like me in higher education. More on that below.
The classification works better as a table than a list:
I’ve seen the campus-consultant relationship personally from at least three perspectives. First, I (or more precisely my IT organization) was a frequent consumer of consultant services, mostly of the General/Limited type for the Implementation purpose. Second, on many occasions I served as a consultant to other campuses, of the Limited/Higher Education type (as a peer) usually for the Advice or Evaluation purposes. Third, at various points my IT organizations were the focus for consultant engagements of the General/Extensive type (McKinsey, PwC, CSC) for the Scrutiny purpose.
So What?
Looking across this landscape, it seems to me that some campus consulting needs are reasonably well served, and some aren’t.
Implementation. This purpose seems reasonably well served, with examples from all four consultant categories. I think this is because campuses are especially likely to seek implementation advice in areas where campuses resemble other entities (for example, parking systems), in which case general consultants can be helpful, or where they resemble other campuses (for example, instructional systems), in which case they prefer higher-education consultants. In either case consultants’ expertise tends to align well with campus circumstances.
Advice. This purpose is a bit less well served. Where campuses resemble other entities or other campuses consultants can be effective. But when advice is needed with regard to policy, or with regard to processes or problems that are more peculiar to higher education, advice from consultants unfamiliar with higher education can be problematic–for example, around security or procurement, where consultants often assume campuses have greater central control over their community and resources than is the case.
Evaluation. The situation here is similar to that for Advice. When the focus of evaluation is generic (that is, has no peculiarly higher-education attributes) and/or the consultant understands a campus’s circumstances outcomes can be good. Otherwise their usefulness can be constrained.
Scrutiny. Most campuses undertake Scrutiny without engaging consultants, relying on administrators and faculty outside the IT organization. This tends to highlight problems and to underrepresent success, since IT tends to be invisible when it’s successful. When campuses seek external help, sometimes they rely on CIOs from other campuses. More typically, they engage General/Extensive firms, use trustee visiting committees, or rely on IT members of accrediting teams. The first two rarely yield useful information, since the firms and committees often do not understand the campus context in which IT operates. This is the same problem that arises when generic outsiders provide Advice or Evaluation. Scrutiny by IT-savvy members of accreditation teams is much the same as relying on CIOs from other campuses ad hoc, and it can produce useful feedback.
Leadership. Campuses can find themselves shorthanded at the CIO level at least four different ways. A CIO may leave abruptly, and so the campus needs interim leadership until he or she is replaced. Similarly, a CIO may be temporarily assigned to other duties on or off campus, yielding a similar need for temporary leadership. A CIO may be temporarily swamped, for example by having to handle a major security breach, a system failure, or a major project. Or a CIO may face problems which he or she is ill equipped to handle, and so require senior-level help. The General/Higher Education firms I mentioned above both provide consulting in this domain, and sometimes campuses draw on particular individuals such as CIOs who have recently retired elsewhere. But overall it’s rare for campuses to use consultants for Leadership purposes, preferring instead to rely on temporary internal promotions or reassignments.
The lacunae I see are three: it appears hard for campuses to find consulting to provide Advice and Evaluation for campus IT overall, to provide productive Scrutiny of IT organization and resources, and to address temporary Leadership needs.
The Personal Note
People like me can fill some of these lacunae. I’ve done that freelance for years, as have many CIO peers from other campuses, often after “retiring”. Most of my own consulting has served Advice, Evaluation, and Scrutiny purposes.
But it’s hard for senior campus leaders to find people like me. And it’s hard for people like me to organize ourselves, especially in collaboration with complementary peers, to ensure that we stay in touch with current IT and campus thinking, that we market ourselves effectively, and that we draw on additional resources and colleagues as necessary. The Educom Consulting Group attempted to do this, but was unable to sustain itself. Collegis, Moran, and other firms that operate within higher-education IT have been more successful, but much of their success has been with smaller institutions. The lacuna remains.
And so to Fortium Partners, which I was recently invited and agreed to join as a partner. Fortium describes itself as “…an IT turnaround and technology services firm providing world-class IT leadership to clients focused on finding solutions to complex IT infrastructure issues or difficult-to–solve operational challenges.” Fortium Partners is modeled on Tatum Partners, a CFO-focused enterprise. In effect, it’s a co-op comprising people like me, except not just from higher education. I hope for two outcomes from this new venture: Interesting projects for me to work on, including some that take me into new domains, and a new resource for those work within and oversee IT on college and university campuses.
If, having read this, you’re thinking “hey, maybe Greg could be helpful,” drop me a line: greg.jackson@fortiumpartners.com



 On the informal agenda, a bunch of us work behind the scenes trying to persuade two existing higher-education IT entities–
On the informal agenda, a bunch of us work behind the scenes trying to persuade two existing higher-education IT entities–
 Most everyone appears to agree that having two competing national networking organizations for higher education wastes scarce resources and constrains progress. But both NLR and Internet2 want to run the consolidated entity. Also, there are some personalities involved. Our work behind the scenes is mostly shuttle diplomacy involving successively more complex drafts of charter and bylaws for a merged networking entity.
Most everyone appears to agree that having two competing national networking organizations for higher education wastes scarce resources and constrains progress. But both NLR and Internet2 want to run the consolidated entity. Also, there are some personalities involved. Our work behind the scenes is mostly shuttle diplomacy involving successively more complex drafts of charter and bylaws for a merged networking entity.


















 “There are two possible solutions,” Hercule Poirot says to the assembled suspects in Murder on the Orient Express (that’s p. 304 in
“There are two possible solutions,” Hercule Poirot says to the assembled suspects in Murder on the Orient Express (that’s p. 304 in  The straightforward projection, analogous to Poirot’s simpler solution (an unknown stranger committed the crime, and escaped undetected), stems from projections how institutions themselves might address each of the IT domains as new services and devices become available, especially cloud-based services and consumer-based end-user devices. The core assumptions are that the important loci of decisions are intra-institutional, and that institutions make their own choices to maximize local benefit (or, in the economic terms I mentioned in
The straightforward projection, analogous to Poirot’s simpler solution (an unknown stranger committed the crime, and escaped undetected), stems from projections how institutions themselves might address each of the IT domains as new services and devices become available, especially cloud-based services and consumer-based end-user devices. The core assumptions are that the important loci of decisions are intra-institutional, and that institutions make their own choices to maximize local benefit (or, in the economic terms I mentioned in  One clear consequence of such straightforward evolution is a continuing need for central guidance and management across essentially the current array of IT domains. As I tried to suggest in
One clear consequence of such straightforward evolution is a continuing need for central guidance and management across essentially the current array of IT domains. As I tried to suggest in  If we think about the future unconventionally (as Poirot does in his second solution — spoiler in the last section below!), a somewhat more radical, extra-institutional projection emerges. What if Accenture, McKinsey, and Bain are right, and IT contributes very little to the distinctiveness of institutions — in which case colleges and universities have no business doing IT idiosyncratically or even individually?
If we think about the future unconventionally (as Poirot does in his second solution — spoiler in the last section below!), a somewhat more radical, extra-institutional projection emerges. What if Accenture, McKinsey, and Bain are right, and IT contributes very little to the distinctiveness of institutions — in which case colleges and universities have no business doing IT idiosyncratically or even individually? Despite changes in technology and economics, and some organizational evolution, higher education remains largely hierarchical. Vertically-organized colleges and universities grant degrees based on curricula largely determined internally, curricula largely comprise courses offered by the institution, institutions hire their own faculty to teach their own courses, and students enroll as degree candidates in a particular institution to take the courses that institution offers and thereby earn degrees. As
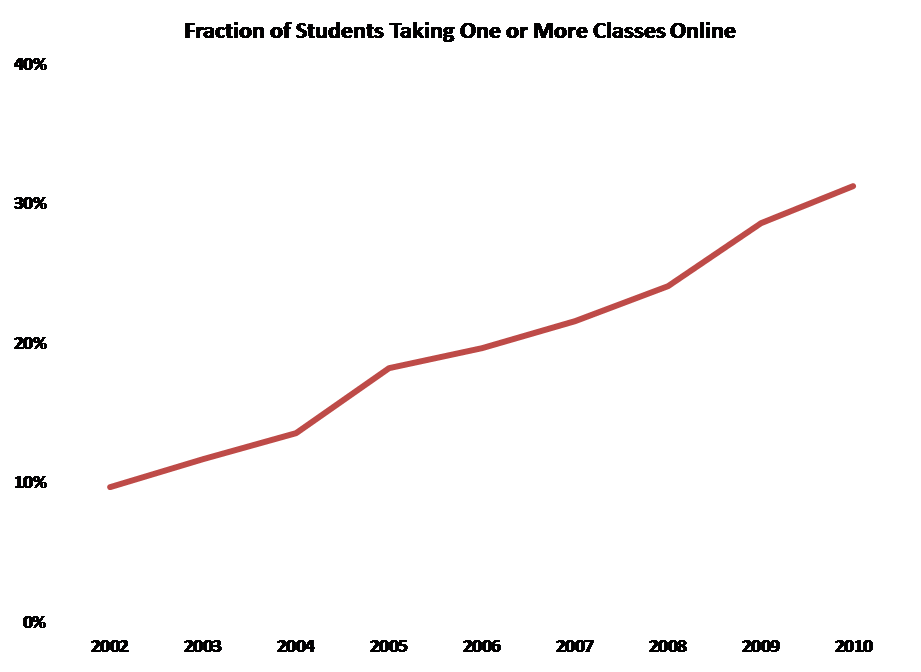
Despite changes in technology and economics, and some organizational evolution, higher education remains largely hierarchical. Vertically-organized colleges and universities grant degrees based on curricula largely determined internally, curricula largely comprise courses offered by the institution, institutions hire their own faculty to teach their own courses, and students enroll as degree candidates in a particular institution to take the courses that institution offers and thereby earn degrees. As  The first challenge, which is already being widely addressed in colleges, universities, and other entities, is distance education: how to deliver instruction and promote learning effectively at a distance. Some efforts to address this challenge involve extrapolating from current models (many community colleges, “laptop colleges”, and for-profit institutions are examples of this), some involve recycling existing materials (Open CourseWare, and to a large extent the Khan Academy), and some involve experimenting with radically different approaches such as game-based simulation. There has already been considerable success with effective distance education, and more seems likely in the near future.
The first challenge, which is already being widely addressed in colleges, universities, and other entities, is distance education: how to deliver instruction and promote learning effectively at a distance. Some efforts to address this challenge involve extrapolating from current models (many community colleges, “laptop colleges”, and for-profit institutions are examples of this), some involve recycling existing materials (Open CourseWare, and to a large extent the Khan Academy), and some involve experimenting with radically different approaches such as game-based simulation. There has already been considerable success with effective distance education, and more seems likely in the near future. As courses relate to curricula without depending on a particular institution, it becomes possible to imagine divorcing the offering of courses from the awarding of degrees. In this radical, no-longer-vertical future, some institutions might simply sell instruction and other learning resources, while others might concentrate on admitting students to candidacy, vetting their choices of and progress through coursework offered by other institutions, and awarding degrees. (Of course, some might try to continue both instructing and certifying.) To manage all this, it will clearly be necessary to gather, hold, and appraise student records in some shared or central fashion.
As courses relate to curricula without depending on a particular institution, it becomes possible to imagine divorcing the offering of courses from the awarding of degrees. In this radical, no-longer-vertical future, some institutions might simply sell instruction and other learning resources, while others might concentrate on admitting students to candidacy, vetting their choices of and progress through coursework offered by other institutions, and awarding degrees. (Of course, some might try to continue both instructing and certifying.) To manage all this, it will clearly be necessary to gather, hold, and appraise student records in some shared or central fashion. Poirot’s second solution to the Ratchett murder (everyone including the butler did it) requires astonishing and improbable synchronicity among a large number of widely dispersed individuals. That’s fine for a mystery novel, but rarely works out in real life.
Poirot’s second solution to the Ratchett murder (everyone including the butler did it) requires astonishing and improbable synchronicity among a large number of widely dispersed individuals. That’s fine for a mystery novel, but rarely works out in real life.