The evil that men do lives after them. The good is oft interred with their bones.
 Lunch with an old friend, beautiful day in Washington, seated outdoors enjoying surprisingly excellent hamburgers. We’re going to talk about our kids, and what we’re doing this summer, and maybe even about working together on a project some day (as we did decades ago).
Lunch with an old friend, beautiful day in Washington, seated outdoors enjoying surprisingly excellent hamburgers. We’re going to talk about our kids, and what we’re doing this summer, and maybe even about working together on a project some day (as we did decades ago).
But as is so often the case for those of us who work in IT, first there’s a technical question about calendars on his iPhone. He’s not clear on the distinction between the iCloud calendar and the one installed by his campus IT group.
I clarify that one is personal and the other enterprise. That segues into a discussion of calendar/email/contacts services (somewhat inexplicably, his campus still uses Notes), and then into IT services and help desks.
My friend observes that his campus provides an excellent array of IT equipment, software (Notes excepted), and services. But it also has one of those “your call will be handled by the next available representative” queuing systems on its IT help desk.
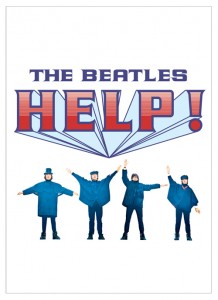
 “I really hate that,” my friend says, as I swipe some of his sweet-potato fries. Because he so dislikes the queuing system, he says, he can’t think positively about his campus’s IT, no matter how good the rest of it is. The evil that men do lives after them; the good is oft interred with their bones. (Why is the Bard on my mind? Because at home we’ve been watching the excellent BBC/PBS Shakespeare Uncovered series on Netflix.)
“I really hate that,” my friend says, as I swipe some of his sweet-potato fries. Because he so dislikes the queuing system, he says, he can’t think positively about his campus’s IT, no matter how good the rest of it is. The evil that men do lives after them; the good is oft interred with their bones. (Why is the Bard on my mind? Because at home we’ve been watching the excellent BBC/PBS Shakespeare Uncovered series on Netflix.)
It’s a familiar refrain. I’ve just been rereading a 1999 article with advice for new CIOs, where I had this to say:
Information technology most often succeeds when it is invisible–when people do not realize they are using it and focus on larger goals. When you and your staff do things right, even spectacularly, no one will notice. This is immensely frustrating. The only comments you are ever going to hear–from the big bosses, from faculty, from staff, from the student newspaper–will be negative, sometimes vitriolically so. This will drive you crazy. No one outside IT at the institution will sympathize.
We like to think this is peculiar to IT. It isn’t.
 Case in point: Registrars. During my tenure at the University of Chicago, we replaced an old terminal-based student system for staff only with a highly flexible, modern web-based system directly accessible by students, faculty, and staff. Students used to wait in line to give their class choices to Registrar clerks, who would then set class lists and enter data in the system manually. Grading, transcripts, and other processes were similar. No one was happy except the Registrar, whose staff and budget necessarily remained large.
Case in point: Registrars. During my tenure at the University of Chicago, we replaced an old terminal-based student system for staff only with a highly flexible, modern web-based system directly accessible by students, faculty, and staff. Students used to wait in line to give their class choices to Registrar clerks, who would then set class lists and enter data in the system manually. Grading, transcripts, and other processes were similar. No one was happy except the Registrar, whose staff and budget necessarily remained large.
The new system (now-defunct SCT‘s now-defunct Matrix product) changed everything: no more waiting in line, simpler scheduling, later deadlines for grades, online transcript requests, you name it. Asked about specifics, almost everyone described almost everything as better.
But no one seemed to feel any better about the University than they had before.
![]()
![]()
![]()
 At lunch, my friend pointed to this apparent conundrum as an interesting parallel to “two-factor theory,” the suggestion by Frederick Herzberg that job satisfaction and job dissatisfaction are independent of each other. The Registrar’s customers were less dissatisfied, but that did not mean they were more satisfied.
At lunch, my friend pointed to this apparent conundrum as an interesting parallel to “two-factor theory,” the suggestion by Frederick Herzberg that job satisfaction and job dissatisfaction are independent of each other. The Registrar’s customers were less dissatisfied, but that did not mean they were more satisfied.
Messier case in point: Business travel. Time was, one made business-travel arrangements by calling (or having one’s assistant call) a travel agency or travel office to make reservations and get a travel advance, and one accounted for the advance and/or got reimbursed for out-of-pocket expense by filling out (or having one’s assistant fill out) a form, attaching paper receipts to it, mailing it somewhere, and eventually receiving a check.
 Today it’s much more typical to make one’s own reservations through an employer-provided website, to pay expenses with a credit card that charges the employer directly, to account for expenses through the same dedicated website, and to have any reimbursement deposited directly. This all goes much faster, and is much more cost-effective for the employer.
Today it’s much more typical to make one’s own reservations through an employer-provided website, to pay expenses with a credit card that charges the employer directly, to account for expenses through the same dedicated website, and to have any reimbursement deposited directly. This all goes much faster, and is much more cost-effective for the employer.
For those of us who like rolling our own, it’s also much more appealing. But for those who don’t, and who don’t have assistants, it’s more awkward and burdensome.
We implemented a modern travel system (Concur) while I was at UChicago. I know anecdotally that most users liked its speed and convenience, but the public reaction consisted largely of complaints (most of which really weren’t about the travel system, but rather about the loss of departmental secretaries as the University did away with them in favor of centralized clerical support).
Coincidentally, my current employer switched to Concur from a paper-based system shortly before I arrived, and I observe the same pattern: widespread private appreciation completely overwhelmed by isolated objection (much of which is actually about changes in policy, such as having to justify non-preferred hotels, rather than the system itself).
 What to do? For the most part we can’t use Mark Antony’s technique: through sarcasm (“Brutus is an honourable man“–imagine the air quotes), he discredits assertions of Caesar’s evil. However, it’s unwise for us to treat our customers’ complaints sarcastically.
What to do? For the most part we can’t use Mark Antony’s technique: through sarcasm (“Brutus is an honourable man“–imagine the air quotes), he discredits assertions of Caesar’s evil. However, it’s unwise for us to treat our customers’ complaints sarcastically.
Rather, a principal strategy for those of us in domains where dissatisfaction automatically overwhelms satisfaction must be to minimize the former. For example, I wrote,
One way to gain unproductive visibility is by unnecessarily constraining choice. To avoid this, wherever possible use carrots rather than sticks to encourage standardization, so that homogeneity is the product of aggregated free choice rather than central mandate… Try to keep institutional options open. Avoid strategies, vendors, architectures, and technologies that constrain choice. Seek interoperability. Wherever possible, have spillover vendors… Think carefully ahead about likely small disasters, many of which are caused by backhoes doing minor excavation, contractors oblivious to wiring closets, incompetent hacking, vandalism, or broken pipes.
But although minimizing unproductive visibility is important, it’s not enough. Mark Antony didn’t rely entirely on discrediting Brutus; he also cited Caesar’s good:
He was my friend, faithful and just to me… He hath brought many captives home to Rome, whose ransoms did the general coffers fill… When that the poor have cried, Caesar hath wept…
Mark Antony understood that discrediting Brutus and extolling Caesar aren’t the same thing. But it was necessary for him to do the former in order to succeed at the latter.
So let it be with IT. We need to recognize more explicitly that maximizing the good things we in IT do to satisfy our customers and campuses (or other organizations) is important, but those good things are different from and do not counterbalance the unproductively visible ways we dissatisfy them.

 the traveler bought, say, a drink for someone, and whereas the expense-reporting policy allows and requires no receipts for taxi fares under $25 or so, it doesn’t allow buying drinks.
the traveler bought, say, a drink for someone, and whereas the expense-reporting policy allows and requires no receipts for taxi fares under $25 or so, it doesn’t allow buying drinks.